
In a world where digitalisation and connectivity are paramount, CISOs need to tackle new frontiers, reinventing their legacy cyber security frameworks as they go. A global economy has meant that CISOs need to ensure they can meet ever-changing, overlapping regulatory standards, and comply and protect their businesses in the best way they can.
CISOs are experiencing higher demands in these evolving environments, where they collaborate with new stakeholders, from engineering team to the CEO. Cybersecurity is no longer just an issue to be dealt with by the IT experts, as Board members now recognise the impact of security across the wider business.
There has never been a better time to increase long-term awareness, by shifting from the conventional ways to more creative training programs, maintaining employee visibility through innovative technology for the monitoring and enhancement of security networks.
Summary
The Benelux Information Security Network enables CISOs, from the largest organisations in the Benelux region, to discuss their current challenges, collaborate and share their experiences to maximise their security defences.
As cyber attacks become increasingly sophisticated and aggressive, CISOs have had to adapt to new challenges, including incorporating new technology into security measures, ransomware attacks, and revising measures of success for security controls. Not only are CISOs having to adopt new approaches to strengthening security networks in all working environments, but they are also having to implement new strategies to raise security awareness among employees to ensure security breaches are swiftly addressed and rectified.
As CISOs continue to invest in training schemes and initiatives to expand the cyber security skills and abilities of their teams, new recruitment and retention policies will be needed to increase the cyber resilience of workforces.
CISOs representing many industries will gather to share their experiences and plans for dealing with challenges and mitigating risks in 2024 and beyond.
Time is maximised onsite through a combination of: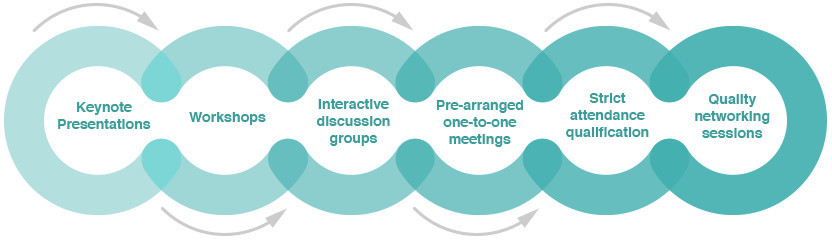
Topics
covered
Partnering with your CCO to better understand business aims and obstacles
Re-evaluating strategies for company-wide clarity in the fight against systemic invasion
Setting values for a security-conscious workforce
Hands-on team building for future organisational security
Building an industry-leading security culture through staff retainment and training
Intimate manoeuvring of company goals to maintain live business monitoring
Condensing your SOC