

With the advantages businesses have seen from going through Digital Transformation and the latest digital technology innovations comes the explosion of data volume and speed of exchange. Cyber threats continually evolve at a rapid rate and businesses will always face a plethora of attacks, no matter how secure they are, hackers will always find a way – inside or out.
Summary
The modern-day security leader strives to reduce complexity across their organisation’s security systems, improve detection and responses to threats, and work across all departments to ensure organization-wide security. With new regulation standards to comply with, upholding security measures has never been more critical.
With emerging technologies, including AI and cloud infrastructures, providing an ideal opportunity to utilise digital innovation to strengthen security measures, CISOs will need to secure buy-in from senior leaders as well as additional resources to make the best use of new developments in information security.
Attendees from a wide range of organisations will be able to share best practise in implementing security measures and encourage cross-sector collaboration to strengthen information security controls.
Time is maximised onsite through a combination of: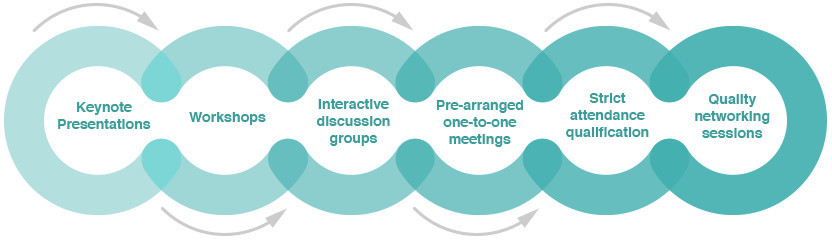
Topics
covered
WFH vulnerabilities: How to adapt to the new way of working & strengthen your defence
Ways to identify, monitor & mitigate third party risks
IT & OT: Integrating both worlds to achieve robust security infrastructure
Attracting & retaining the next generation of cyber security experts
Using behavioral analytics to detect vulnerabilities
How has the global pandemic shaped the role of the CISO?
Speaking the language of business to achieve board buy-in
Preparing for the emerging threat landscape
Ways to secure your applications
Migrating to cloud & unlocking its full value
How to optimally detect & neutralize threats, including ransomware attacks, in real-time
The state-of-the-art technology to implement by the year 2030